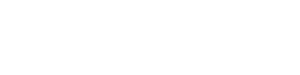
Your event deserves more than a webinar
Captivate your attendees with an immersive 3D world, allowing them to effortlessly navigate your virtual venue, connect seamlessly with others, and deeply engage with your content.

Your world, with one click
Discover five immersive environments for personalized journeys: alpine lodge, island resort, luxury hotel, conference center, or event facility. Your dream destination is just a click away!
Engaging lifelike visuals
Experience awe-inspiring photo-realism in our virtual event venues. No VR goggles, downloads, or powerful gaming machines required.
Easy access and retention
Each 3D venue offers diverse, lifelike locations for easy access to live streams, meeting links, videos, and PDFs, all complemented by branded signage.

Create meaningful connections
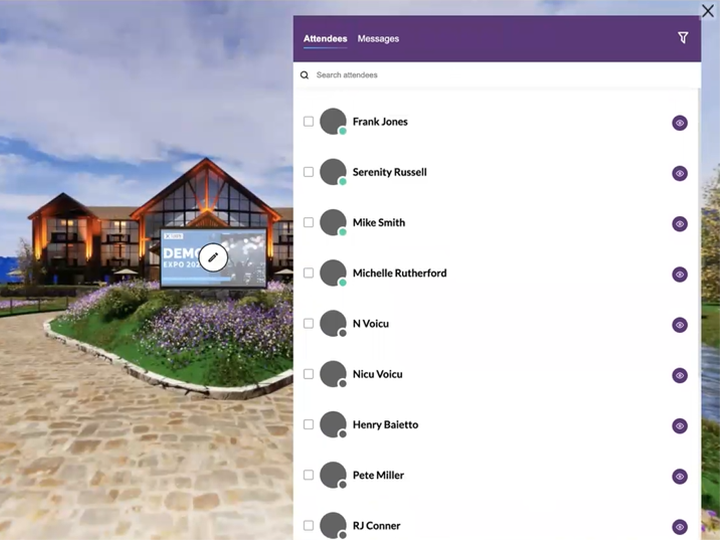
Network with ease
Effortlessly find and connect with others at your event using attendee presence detection and affinity field searching.
Streamline Connections
OmniChat™ empowers your attendees with impromptu text, voice, or video chats, allowing them to initiate 1:1 or group conversations on the fly; no meeting invites needed.
Manage OmniChat™ sessions during or after events
Empower your attendees to handle multiple online conversation threads, including saving the chat text, even while keynote or breakout sessions are in progress.
Powerful and easy to use
Create landing pages with ease
Create and modify your event landing pages swiftly with our WYSIWYG (What You See Is What You Get) editor.
Pre-configure for a stress-free launch
Prep, schedule, and test your event elements (landing page, agenda, content, and signage) in advance.
Leverage host event analytics
Discover insights into attendee behaviors and content engagement with our robust analytics engine, revealing trends, patterns, and key moments.
"*" indicates required fields







